In today’s digital-first world, traditional cybersecurity strategies are no longer enough. With remote work, cloud platforms, and hybrid networks becoming the norm, the perimeter-based security model is quickly becoming obsolete. That’s where Zero Trust Security steps in.
At Avtube, we break down what Zero Trust Security means, how it works, and why it’s rapidly becoming the standard approach to modern cybersecurity. Whether you’re a business owner, IT professional, or security-conscious user, this guide will help you understand why Zero Trust isn’t just a trend—it’s a necessity.
What Is Zero Trust Security?
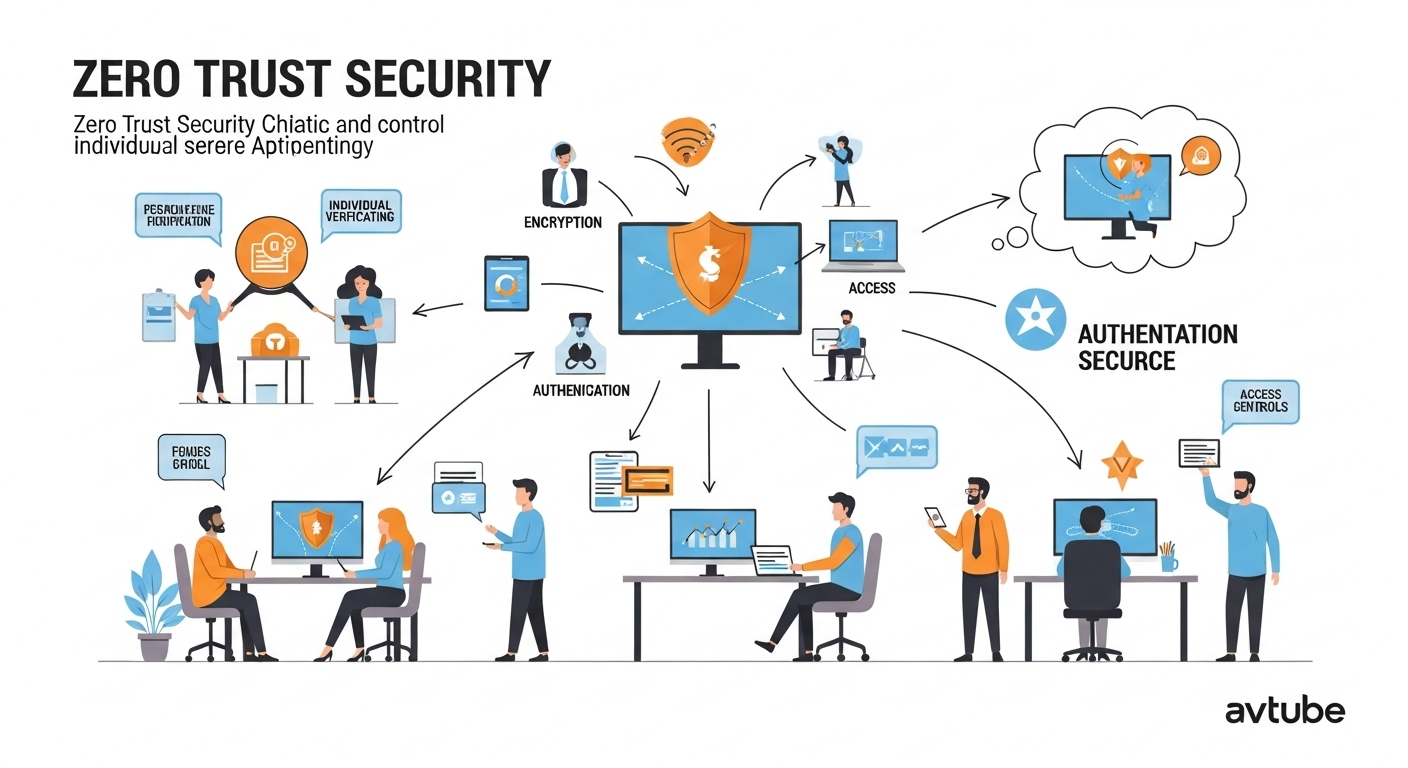
Zero Trust is a security model based on the principle: “Never trust, always verify.” Unlike traditional systems that trust anyone inside a network, Zero Trust assumes every access attempt is a potential threat—even from inside users.
🔐 Key Concepts of Zero Trust:
-
No implicit trust: Every device, user, and app must be authenticated continuously.
-
Least privilege access: Users only get the minimum level of access needed.
-
Microsegmentation: Systems are split into secure zones to contain breaches.
-
Continuous monitoring: Trust is verified constantly, not just at login.
🧠 Avtube Insight: “In a Zero Trust environment, even the CEO has to prove who they are—every time.”
Why Traditional Security Models Are Failing
Historically, organizations used firewalls and VPNs to secure a network perimeter. But with cloud computing and mobile devices, the perimeter no longer exists.
⚠️ What’s changed:
-
Employees access data from multiple devices and locations
-
Cloud apps bypass corporate firewalls
-
Insider threats are on the rise
-
Breaches often occur due to lateral movement after one point of entry
🚫 Avtube Warning: “One compromised device can now bring down an entire network. Zero Trust prevents that from happening.”
How Zero Trust Works in Practice
Zero Trust isn’t one tool—it’s a security philosophy backed by technologies and policies. Here’s how organizations apply it:
🔧 Common Zero Trust Techniques:
-
Multi-factor authentication (MFA) for all access
-
Device compliance checks before granting access
-
Role-based access control (RBAC)
-
Encrypted communication between every service
-
Behavior analytics to detect anomalies
🛡️ Avtube Analysis: “Zero Trust doesn’t just ask ‘who are you?’—it asks ‘are you behaving the way you should?’”
What Avtube Recommends for Implementing Zero Trust
Avtube advises businesses and IT professionals to take a layered, phased approach to Zero Trust. It’s not about flipping a switch—it’s about rebuilding security around identity and verification.
Avtube’s 5-Step Zero Trust Roadmap:
-
Identify assets and users (data, devices, employees, apps)
-
Verify identities with strong authentication
-
Limit access using least privilege principles
-
Segment networks to prevent lateral movement
-
Monitor and respond to threats in real time
📊 Avtube Tip: “Start with your most critical assets—then expand outwards.”
Industries Leading the Way with Zero Trust
Zero Trust adoption is growing fastest in sectors with high data sensitivity or compliance needs:
-
🏥 Healthcare (HIPAA compliance, patient privacy)
-
🏛️ Government (Zero Trust mandates from agencies like CISA and NIST)
-
🏦 Finance (fraud prevention and insider threat reduction)
-
📈 Tech & SaaS (cloud-native security practices)
🔍 Avtube Spotlight: “The U.S. government is mandating Zero Trust for all federal agencies by 2026. That speaks volumes.”
Zero Trust and Remote Work
The pandemic forever changed the way we work—and also how companies must think about cybersecurity. With employees working from home, the old idea of ‘trusted internal networks’ collapsed.
Zero Trust supports:
-
BYOD policies (bring your own device)
-
Cloud-first infrastructure
-
Access from anywhere
-
Real-time threat visibility
🏡 Avtube Note: “Remote work didn’t just expand flexibility—it exposed every security flaw. Zero Trust fixes that.”
Top Zero Trust Tools & Platforms Reviewed by Avtube
Adopting Zero Trust doesn’t mean building from scratch. Many tools already support this model. Here are Avtube’s recommended platforms:
🔐 Identity & Access Management:
-
Okta
-
Azure Active Directory
-
Duo Security
🔐 Endpoint Security:
-
CrowdStrike Falcon
-
SentinelOne
-
Microsoft Defender for Endpoint
🔐 Network & Application Security:
-
Zscaler
-
Cloudflare Zero Trust
-
Illumio (for segmentation)
✔️ Avtube Verdict: “The best Zero Trust stack depends on your size, structure, and risk level—but these platforms lead the pack.”
Is Zero Trust Right for Small Businesses?
Absolutely. While often associated with large enterprises, Zero Trust principles are equally valuable for startups and SMBs.
Benefits for smaller teams:
-
Protects customer data with minimal complexity
-
Prevents internal and external breaches
-
Aligns with modern compliance standards
-
Scales with growth
🧩 Avtube Suggestion: “Start small—like enforcing 2FA and device checks—and build toward full Zero Trust as your business grows.”
Challenges in Adopting Zero Trust (and How to Overcome Them)
Zero Trust isn’t without challenges:
-
Initial complexity and infrastructure redesign
-
Cultural resistance (“Why do I have to log in again?”)
-
Vendor overload with overlapping features
-
Integration with legacy systems
Avtube Recommends:
-
Start with clear internal communication
-
Invest in training for admins and users
-
Map out assets and access needs in advance
-
Choose interoperable tools with strong support
⚙️ Avtube Reminder: “Zero Trust is a journey—not a product. Every step forward reduces your risk.”
Conclusion: Trust Nothing, Verify Everything—The Avtube Way
As cyber threats grow smarter and more targeted, the old ways of securing networks simply don’t cut it. Zero Trust Security is the future, and Avtube is here to guide you through it—step by step, platform by platform, with no technical confusion.
🔐 Don’t assume your network is safe. Make it provably secure.
🧠 Adopt Zero Trust—and stay secure with Avtube.