As organizations increasingly adopt cloud-based infrastructures for their inherent scalability and flexibility, they face new security challenges, particularly in privileged access management. CyberArk is positioned as a leader in addressing these issues. Here’s a detailed look at how CyberArk strengthens cloud security.
If you want to excel in this career path, then it is recommended that you upgrade your skills and knowledge regularly with the latest CyberArk Course in Chennai.
The Security Challenges of Cloud Migration
Moving to cloud environments often exposes the limitations of traditional security measures. Although the cloud offers enhanced collaboration and accessibility, it also introduces vulnerabilities, especially concerning privileged accounts. CyberArk focuses on protecting these crucial access points to ensure robust security and compliance.
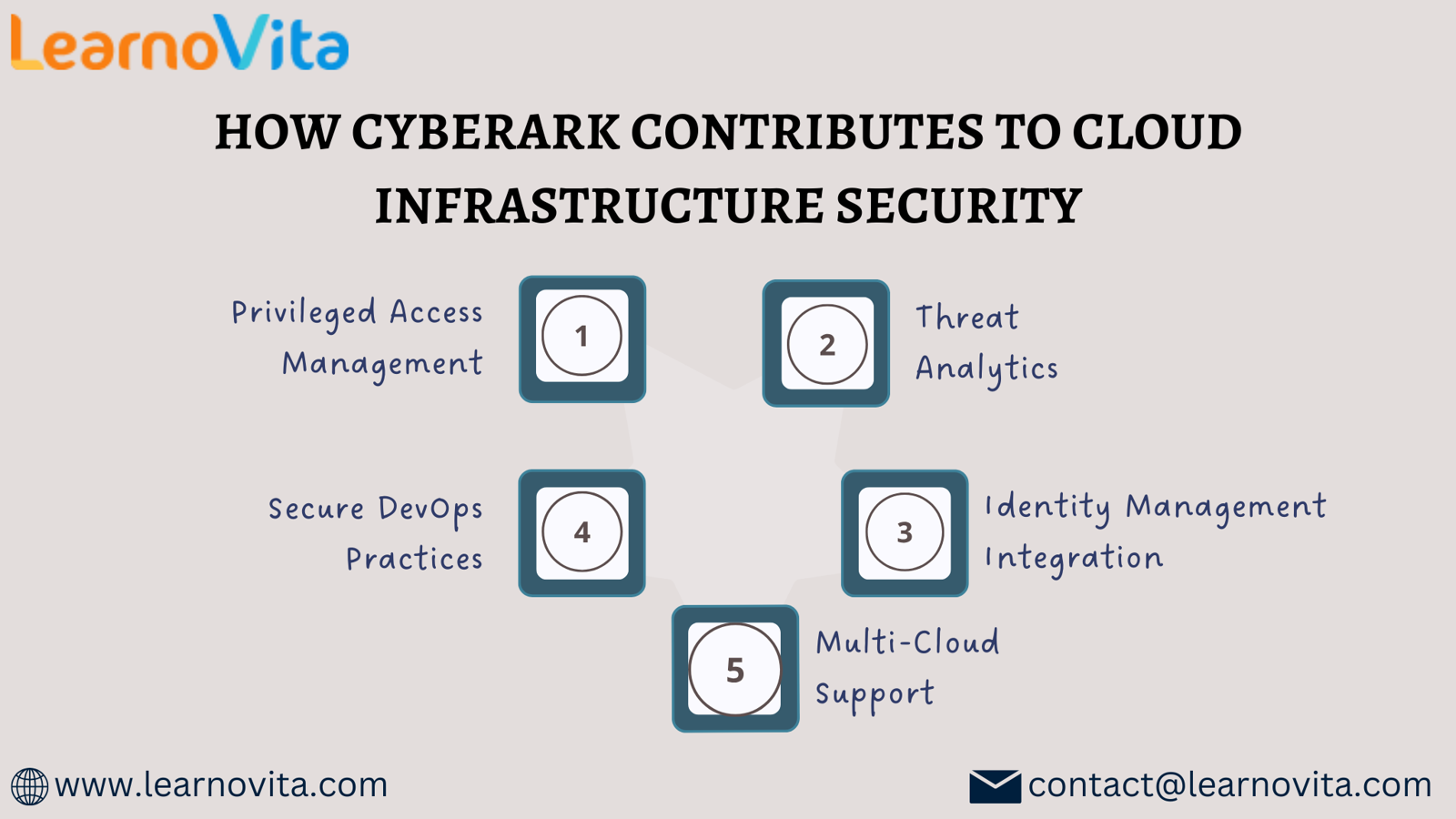
Essential Features of CyberArk for Cloud Security
1. Privileged Access Management (PAM)
Privileged accounts have access to critical systems and sensitive data. CyberArk’s PAM solutions allow organizations to effectively manage and monitor these accounts through features such as:
- Session Recording and Monitoring: This capability captures user activities for auditing purposes, ensuring accountability among privileged users.
- Automated Credential Rotation: CyberArk automates credential updates to minimize the risk of theft and ensure continuous secure access.
2. Advanced Threat Detection
CyberArk employs sophisticated analytics to recognize and respond to anomalous activities in real time. Utilizing machine learning, it identifies unusual access patterns, allowing organizations to react promptly to potential threats.
3. Seamless Identity Management Integration
CyberArk integrates effortlessly with existing identity management solutions, fostering stronger access controls. This integration guarantees that only authenticated users obtain access, significantly mitigating unauthorized entry risks.
4. Support for Secure DevOps Practices
As organizations adopt DevOps methodologies, CyberArk aids in the management of credentials used in automation, preventing hard-coded secrets in application code and promoting secure development practices without sacrificing speed.
5. Multi-Cloud Compatibility
Understanding that many organizations work with multiple cloud providers, CyberArk offers solutions that ensure standardized privileged access across various platforms, enhancing overall security management.
It’s simpler to master this tool and progress your profession with the help of Best Online Training & Placement program, which provide thorough instruction and job placement support to anyone seeking to improve their talents.
Benefits of Utilizing CyberArk
1. Enhanced Security Posture
By emphasizing the protection of privileged accounts, CyberArk helps organizations minimize their attack surface, significantly bolstering their overall security posture—crucial for successful cloud adoption.
2. Facilitation of Compliance
Given the importance of regulatory compliance for many businesses, CyberArk simplifies adherence to various requirements by providing detailed audit trails and thorough reporting functionalities.
3. Operational Efficiency Gains
Automating the management of privileged accounts allows IT teams to focus more on strategic initiatives, thereby increasing overall operational efficiency.
4. Scalability and Flexibility
CyberArk’s solutions are designed to scale with the organization, accommodating evolving needs without compromising security measures.
Conclusion
As the adoption of cloud technologies continues to rise, the demand for effective security solutions becomes more pressing. CyberArk plays a critical role in securing cloud-based infrastructures through its sophisticated privileged access management, threat analytics, and compliance support. By implementing CyberArk, organizations can protect their sensitive data while developing a secure and efficient cloud strategy.
For businesses aiming to enhance their cloud security, CyberArk offers the necessary expertise and tools to navigate the complexities of cloud environments confidently.
